Chris Lees recently published research into decrypting the MEGA megaprefences database, and went further by releasing a script to automate the process. This was truly excellent work, and generous to share this with the community.
With his permission, I’ve adapted his script, added in some extra nuggets from some research, and provide some validation below.
Further research
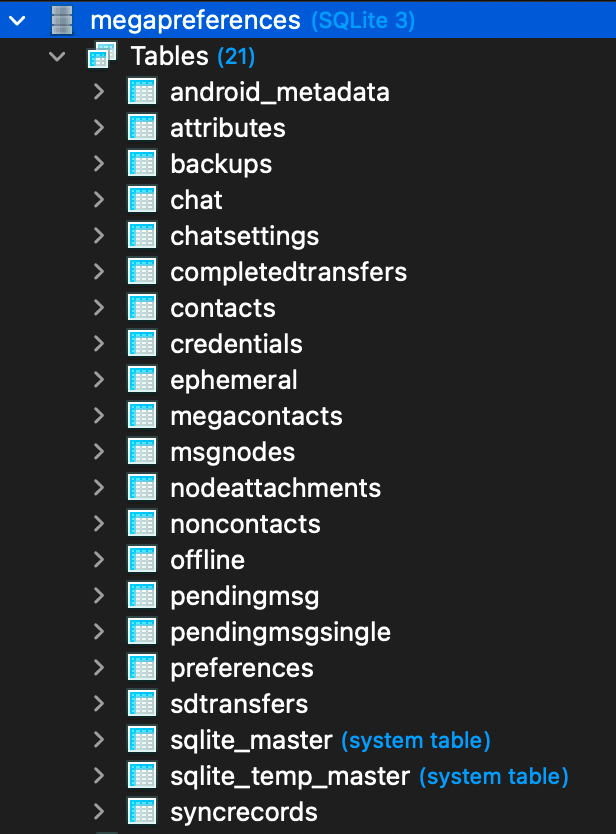
Within the megapreferences database is the completedtransfers table.
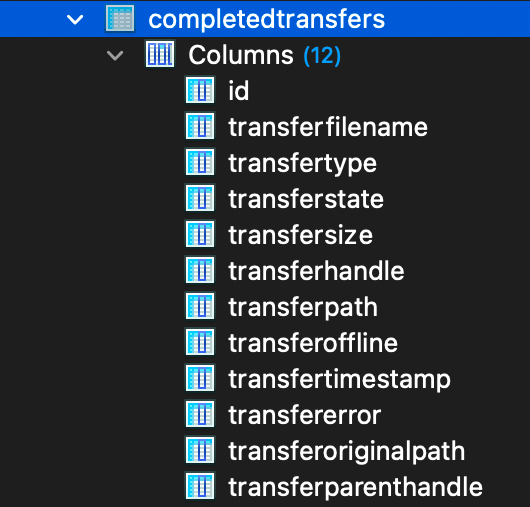
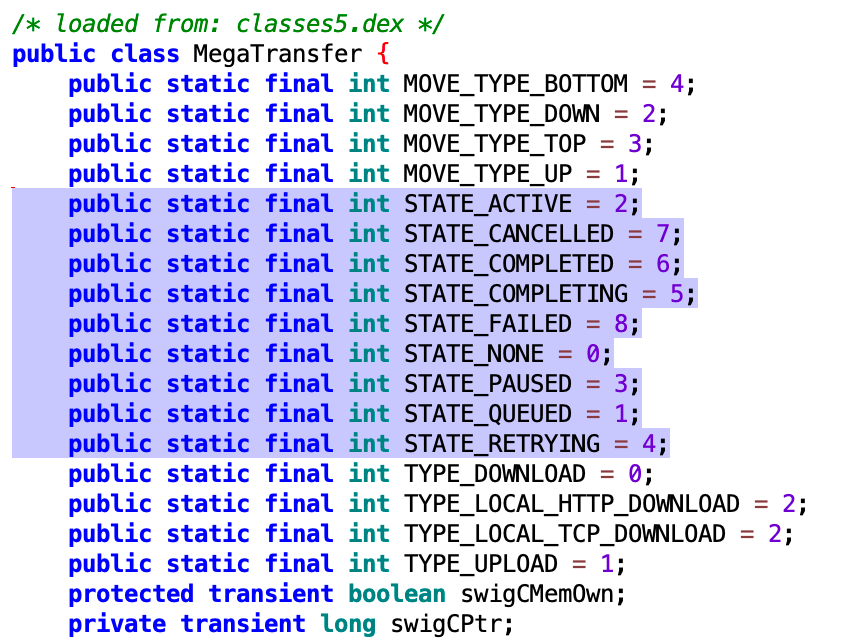
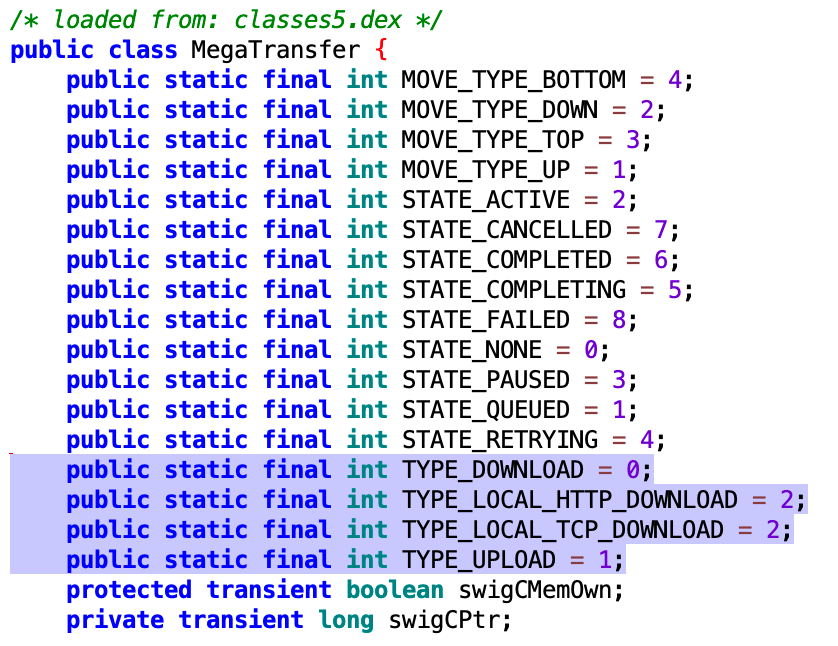
Many of the column names and values are straight forward, but a couple need some clarification. State and Type.
Examining the application code (decompiled using jadx-gui), a number of keys and values can be found relating to transferstate and transfertype.
ALEAPP
Bringing this all together, the artefact submitted to ALEAPP will look something like the below.

Validation
Let’s examine a few of these records. Below is a comparison of the artefact versus notes made whilst populating data.
Item 1
A plain upload to the MEGA cloud storage.
| Timestamp | App | Subject | Detail |
| 20 Mar 2022 at 10:51 | Camera | Photo | Flowers |
| 20 May 2022 at 09:14 | Mega | Upload | Flowers Photo |
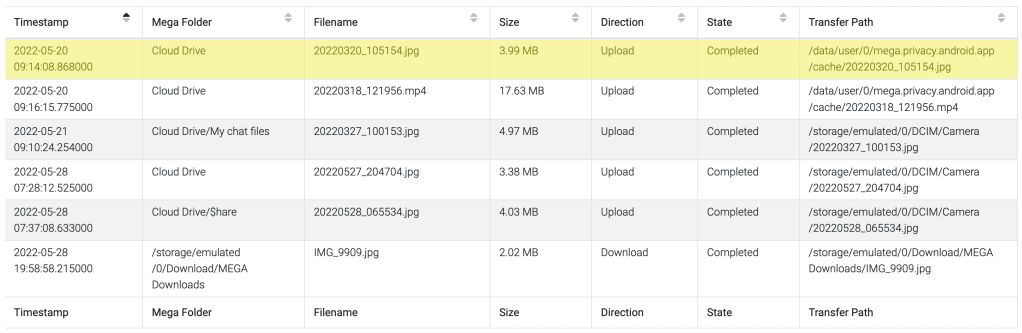
The timestamp of the upload, folder, filename, size, direction and state were all consistent with the original file. The transfer path provides a further artefact.
Item 3
Sending an image via chat.
| Timestamp | App | Subject | Detail |
| 27 Mar 2022 at 10:01 | Camera | Photo | “No unauthorised access” sign |
| 21 May 2022 at 09:09 | Mega | Sent image | “No unauthorised access” sign |
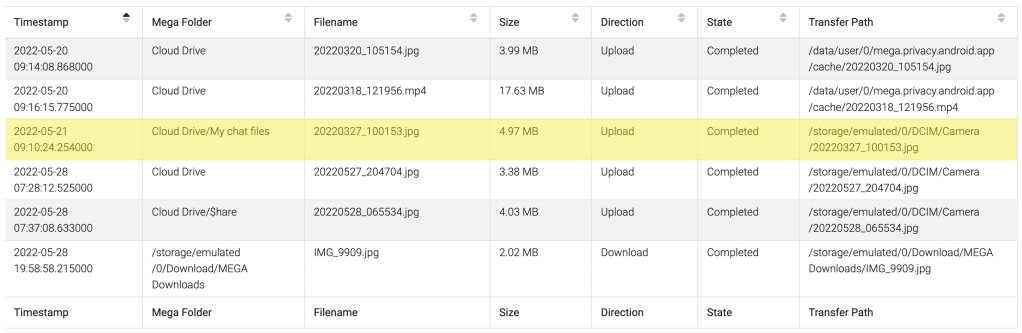
The timestamp of the upload, folder, filename, size, direction and state were all consistent with the original file. This time, the transfer path was the consistent with the original and not a cached file like before.
Item 6
Saving an image recevied via chat.
| Timestamp | App | Subject | Detail |
| 28 May 2022 at 19:48 | Mega | Received image | Tap Photo |
| 28 May 2022 at 19:56 | Mega | Import from Chat | Tap Photo |
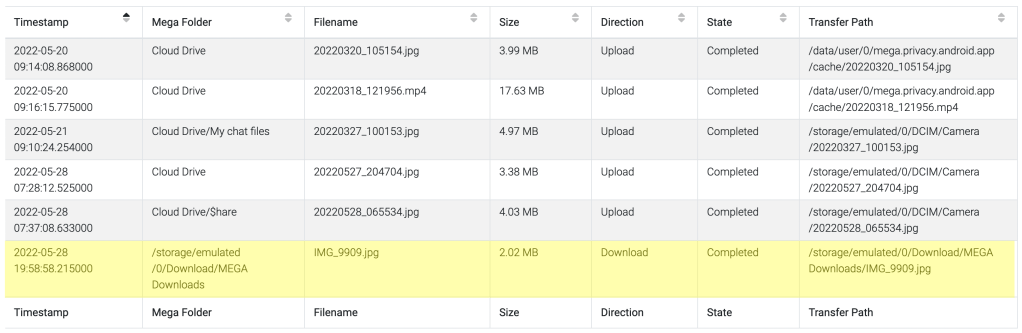
The timestamp was consistent with the download time. The folder was consistent with the destination. The filename reflected the original filename on the senders device. The size, direction and state were consistent. And the transfer path was consistent with the destination.
Closing remarks
I want to reiterate that this is a prime example of standing on the shoulders of giants. Credit should go to Chris Lees for doing the initial research, publishing the decryption method, which is what made this possible.
This artefact has been submitted to ALEAPP, so thanks to Alexis Brignoni for maintaining and the project.
As always, interested in your thoughts and feedback.

One response to “Even more MEGA”
[…] Kibaffo33Even more MEGA […]
LikeLike