Intro to Vaulty
Vaulty is a free app which provides a PIN/password protected secure folder.
Users can upgrade to make use of additional privacy features such as disguising the app.
Usage
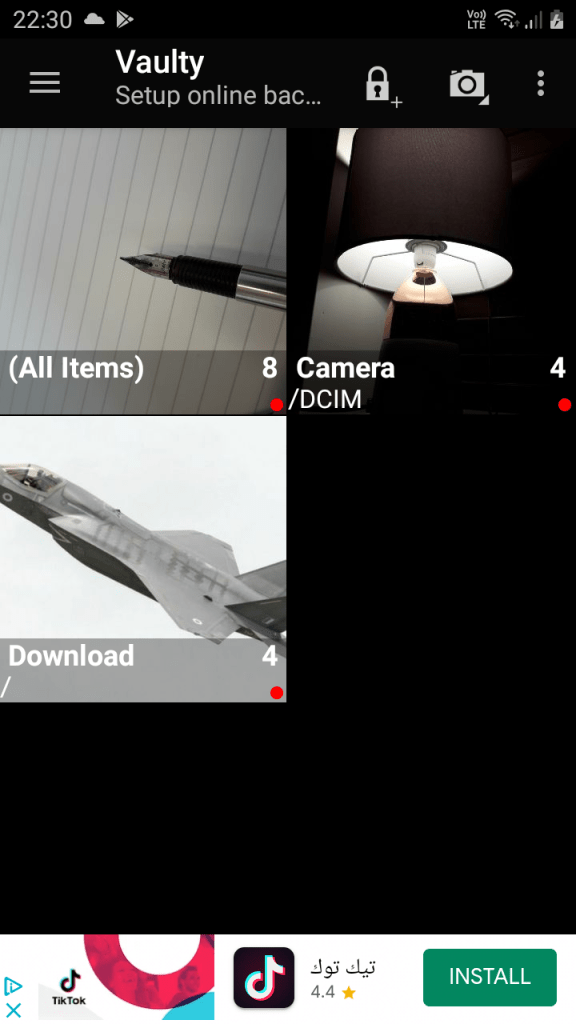
Setting up the app, the user is prompted to configure a PIN, password, or opt to use none. Having set up, entry to the app meets you with the following screen.

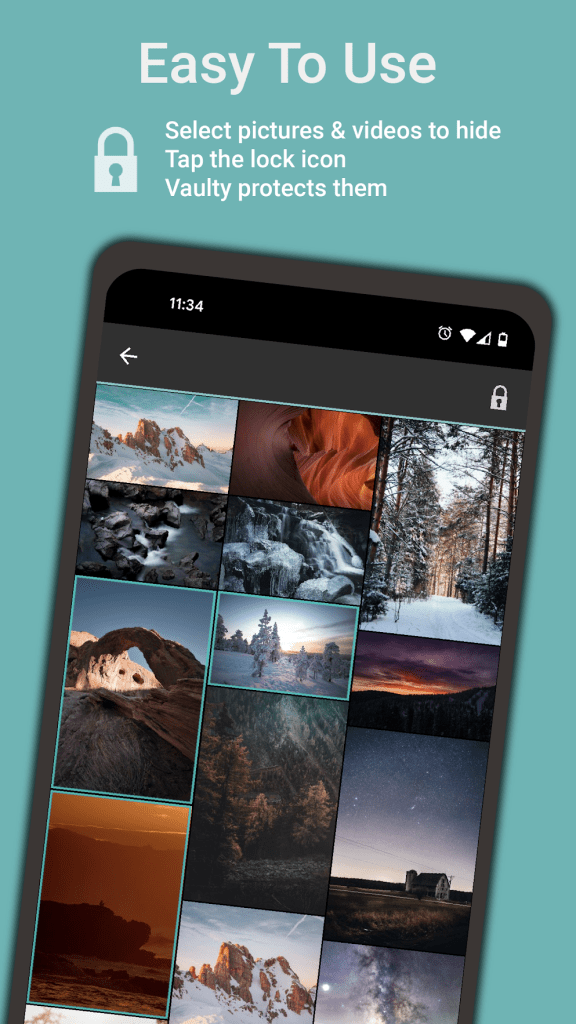
Entry of the correct PIN will lead the user to their vault (as shown below). An incorrect PIN will take a “Mugshot” (photo with user-facing camera) and add it to the Vault under a Mugshots album. Beware examiners!
Data
The application data can be found at the below file path.
/data/data/com.theronrogers.vaultyfreeVaulty files, by default, are stored at the below file path. The user can change this destination by accessing the settings menu.
/storage/emulated/0/Documents/VaultyThe Vaulty database is located at /data/data/com.theronrogers.vaultyfree/databases/media.db. It contains the columns shown below. Many columns held nothing but NULL values when populating with test data.
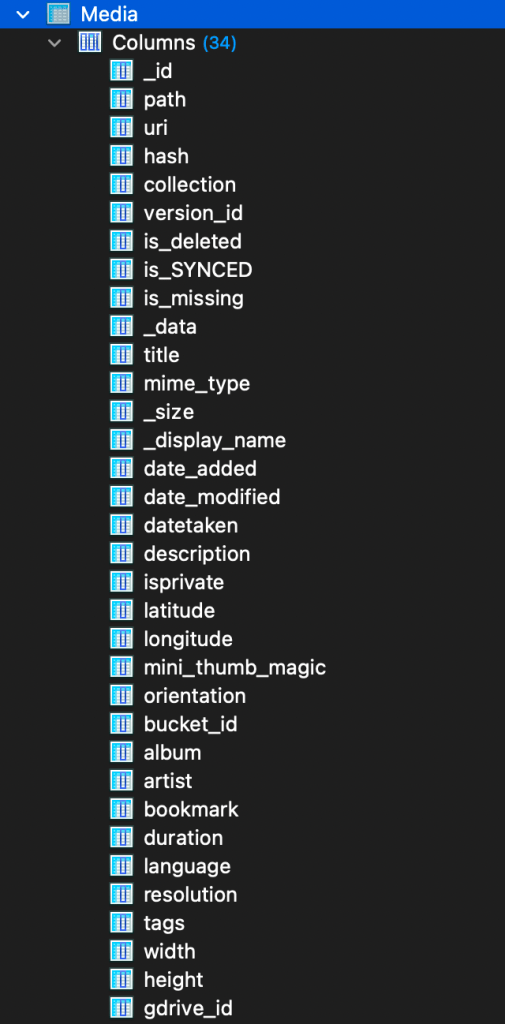
Testing showed the most meaningful columns to be _id, datetaken, date_added, date_modified, path and _data.
That said, the data in the rows didn’t quite match their column headers.
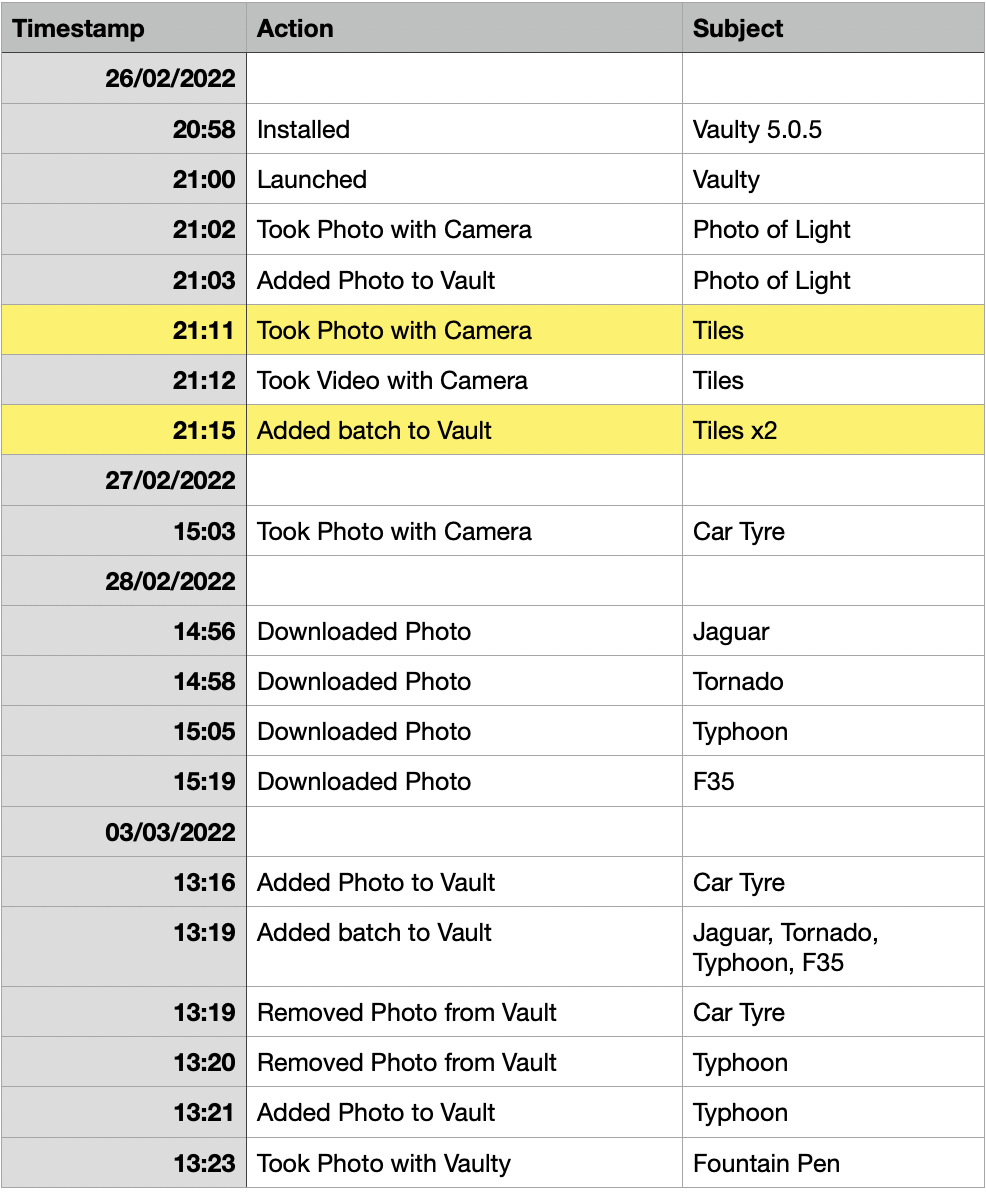
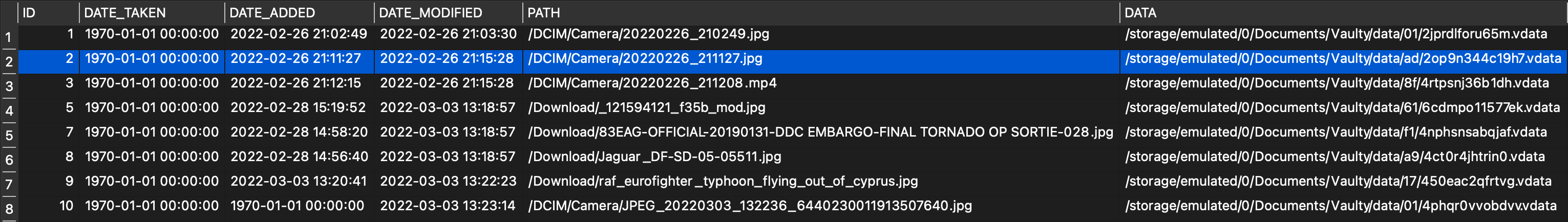
date_added held the creation timestamp of the file, and date_modified held the added-to-vault timestamp of the file.
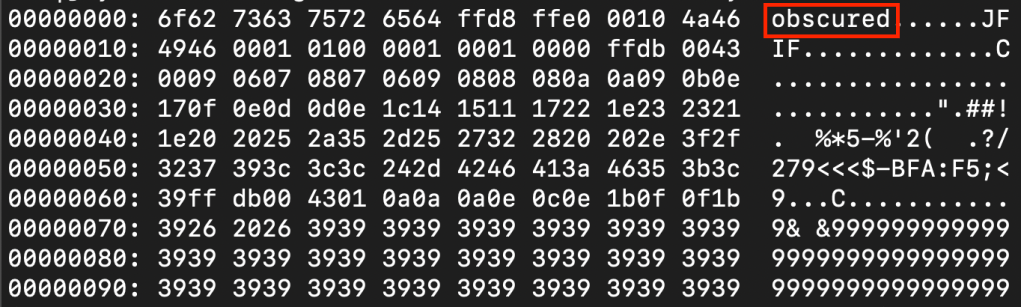
Closer inspection of a vaualted-file showed it had been modified slightly. Not encrypted, but “obscured” by at least inserting a few bytes at offset zero.
The preferences file, at /data/data/com.theronrogers.vaultyfree/shared_prefs/com.theronrogers.vaultyfree_preferences.xml, also holds some interesting data.
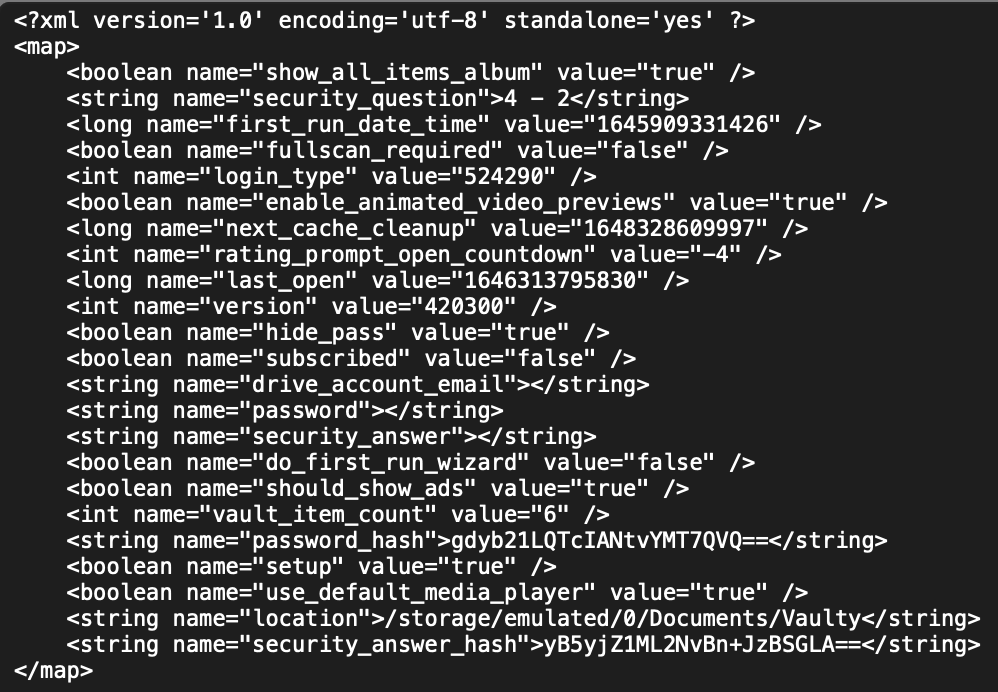
password_hash held a vanilla MD5 hash of the PIN, trivial to brute force.
security_question was in plain text.
location held the vault destination.
Evaluation and notes
Vaulty is a fairly straight forward app for the user and analyst. Decoding was certainly not as fancy as some of the recent posts from theincidentalchewtoy!
Although users might expect to have some encryption, there isn’t any, and in fairness to the developer it certainly doesn’t advertise any. The app simply offers a PIN protected space for files.
The files are modified slightly to remove the header. This may provide obstacle to very rudimentary forensic tools but the image would still be picked up as embedded on anything half decent.
Unvaulted images had a modified MD5 compared to the original.
Vaulty keeps a log file at /data/data/com.theronrogers.vaultyfree/files/internalLog.txt which is worth further analysis.
This decoding has been submitted to ALEAPP, including app info, brute-forcing of 4 and 6 digit PINs, and vault file listing.




One response to “Decoding Vaulty”
[…] Kibaffo33Decoding Vaulty […]
LikeLike